Hacks, lost private keys, data leaks, dead exchange owners—the list of mishaps separating cryptocurrency owners from their savings grows longer almost by the week.
Now, new custodial schemes aim to re-establish trust among digital asset holders and give impetus to the boom in decentralised computing.
‘Own your private keys’
The recent loss of up to $140m in client assets following the death of Gerald Cotten, chief executive of cryptocurrency exchange Quadriga, is the latest in a long list of security breaches affecting owners of digital currencies.
At least $15bn in cryptocurrencies have been stolen from exchanges or other central storage venues since 2013, according to one estimate.
For those concerned about security risks, a standard response amongst cryptocurrency experts is to move the private keys governing access to digital assets into ‘cold storage’.
This means taking those private keys off internet-connected devices and recording them elsewhere, for example on specially designed USB sticks, on pieces of paper or as engravings into metal.
Obsessive secrecy, it seems, is the only way to secure an asset that is ultimately a string of ones and zeros, easy to copy and therefore to steal.
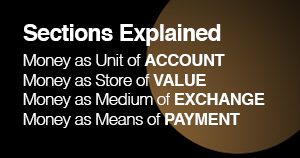
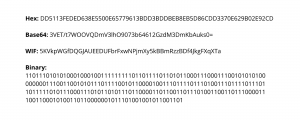
The same bitcoin private key written in four different formats
Everything can be hacked
But computer security experts point out that it’s near-impossible to ensure that your cryptocurrency private keys cannot be stolen.
“Basically, everything can be hacked”
Even devices that have been designed especially to hold these keys are vulnerable, says Stepan Snigirev, a former quantum physicist and co-founder of Crypto Advance, a hardware wallet designer.
Speaking at the recent Advancing Bitcoin 2019 conference in London, Snigirev produced an extensive list of the vulnerabilities of cryptocurrency hardware wallets.
“Basically, everything can be hacked,” said Snigirev.
“You can have supply chain attacks,” he went on. “For example, chips that provide mobile functionality can be replaced. You bribe a Chinese factory to doctor a chip. Or you can change the signing algorithm to reveal private keys.”
“Then, if you manage to get hold of a hardware wallet you can use techniques like voltage glitching or decapping,” Snigirev added.
“Decapping uses a laser cutter to remove the plastic parts of the chip,” he explained.
“You put a few drops of nitric acid on top, heat it up and you can use a microscope to see the position of the secrets. You can find the PIN and the PIN counter using ultraviolet light, or erase parts of the memory to reset the PIN to 0000. It’s pretty hard to deal with such attacks,” he said.
“Throw away the private key and no one can access your holdings”
Software-based cryptocurrency wallets have their own flaws, with the security risks especially acute for the inexperienced, said Jameson Lopp, CTO at cryptocurrency custody firm Casa, speaking at the same event.
“It’s very difficult to design software for newbies,” said Lopp.
“You have to assume the worst when it comes to users: they will do the absolute minimum to get the software working. They will use easily guessable or crackable passwords and then reuse those passwords,” he said.
However, there is one way to ensure total security when using cryptocurrency, said Lopp.
“You just throw away the private key and no one can access your holdings,” he said.
Clients of Quadriga, whose CEO apparently went to his grave with the private keys governing access to their funds, or James Howells, a Welsh IT worker who accidentally threw a hard drive with his bitcoin keys into a Welsh landfill site, losing up to $80m, may struggle to appreciate the humour.
A tiered security approach
Regular users of cryptocurrency may want to rely on a tiered security approach, argues Crypto Advance’s Stepan Snigirev.
“For your everyday expenses, you may be happy to keep a few hundred euros in cryptocurrency on your mobile phone. For your salary, you may want a hardware wallet. But for your life savings, you may want a Shamir secret insurance scheme or a multi-signature set-up,” said Snigirev.
A Shamir scheme involves splitting a cryptocurrency secret, such as the mnemonic phrase used to govern access to a hardware wallet, into parts, and distributing the parts to different locations or people.
As the name suggests, a multi-signature protocol requires the approval of more than one person before a cryptocurrency transaction is processed.
This approach mirrors the redundancy built into nuclear powers’ attack plans: while the exact details are secret, it’s generally accepted that neither President Trump nor President Putin could launch their weapons without the approval of others in the chain of military command.
New trust models
Given the inherent difficulty of balancing security with usability, custody experts are now moving away from the dogmatic advice to hold your own private keys. Instead, new trust models are emerging to help cryptocurrency owners store and spend their money safely.
“Our approach is to minimise trust”
“Our approach is to minimise trust,” said Casa’s Jameson Lopp.
“We do that by pushing security to the edges: we want as many sensitive operations as possible to take place on user-owned hardware devices, ideally on full nodes.”
Casa sells a $300 bitcoin node in the form of a small computer adapted from a Raspberry Pi and a Seagate hard disk drive. The Casa node also works on the Lightning network, the payments infrastructure being built on top of bitcoin.
And Casa provides clients with a mobile app called Keymaster, which can be used to authorise transactions either alone or in conjunction with other devices.
The safer option—requiring multiple signatures to move cryptocurrency, rather than approving transactions from the mobile device alone—means storing one private key on the mobile device, a second on a hardware wallet like a Trezor or Ledger, a third key with Casa itself, and then requiring two of the three private keys to approve a transaction.
While Casa’s product offering appears targeted at the retail user or small business, other new custody ventures are targeting institutional investors in cryptocurrency.
“Cold storage custody is vulnerable to human error”
Anchorage, which calls itself the first crypto-native custody firm, launched its service in January this year. The start-up, which has been backed by prominent Silicon Valley venture capital firms, says it combines a multi-signature protocol with its own behavioural analytics software, which flags for outliers and abnormalities.
In a recent Medium article, Anchorage’s founders, Diogo Mónica and Nathan McCauley, pointed out the range of services institutional investors are likely to require when investing in cryptocurrency.
“Cold storage custody is vulnerable to human error and holds assets inaccessibly so they are slow to move and can’t be used to capture yield, which can lead to depreciation due to dilution over time,” said Mónica and McCauley.
“Our service extends all the benefits of asset accessibility, including capturing yield from staking and inflation, voting, auditing proof of existence, and fast transactions,” they said.
Combating surveillance capitalism
Casa’s chief executive, Jeremy Welch, sees the proliferation of individually owned devices for the storage of digital assets as a critical part of what he calls the fourth computing wave, which he thinks could challenge the business models of today’s internet giants.
“It’s really important that we move away from this centralised data model”
“The entire business model of companies like Facebook and Google is data- and advertising-based,” Welch told attendees at Advancing Bitcoin 2019.
“It’s surveillance capitalism: as these intermediaries have become all-powerful, they’ve started abusing their access to data. It’s really important that we move away from this centralised model,” said Welch.
“Now, Facebook is planning to monetise the metadata from combining Messenger, Instagram and WhatsApp,” Welch pointed out.
Facebook said in January it was planning to merge the three messaging services it owns.
“There’s no guarantee that the resulting metadata will not somehow be compromised,” said Welch.
“And now the stakes are much higher.”
Casa’s CEO says his company’s goal is to improve the safety and usability of customer-owned storage devices for digital assets.
“Beyond the price hype is a computing revolution”
“If encryption and local validation is the way forward, we need to simplify both steps,” said Welch.
“Then we can build computing applications to compete with the old centralised models of key management.”
Cryptocurrency market observers who are focused on the prices of assets like bitcoin and ethereum are in danger of missing the wood for the trees, argues Welch.
“Beyond the price hype is a computing revolution,” he said.
“Manage your keys and get a node. This is the way to participate in the new world we’re building,” Welch told conference attendees.
Want to receive New Money Review’s monthly content updates? Sign up here.